The Latest
Filter by Topic
Filter by Type
Oasys Summit Convenes in Coronado, Debuting First-Ever Awards Program
Taking place across three days, the annual summit tackled topics of building confidence and go-to-market strategies, while offering…
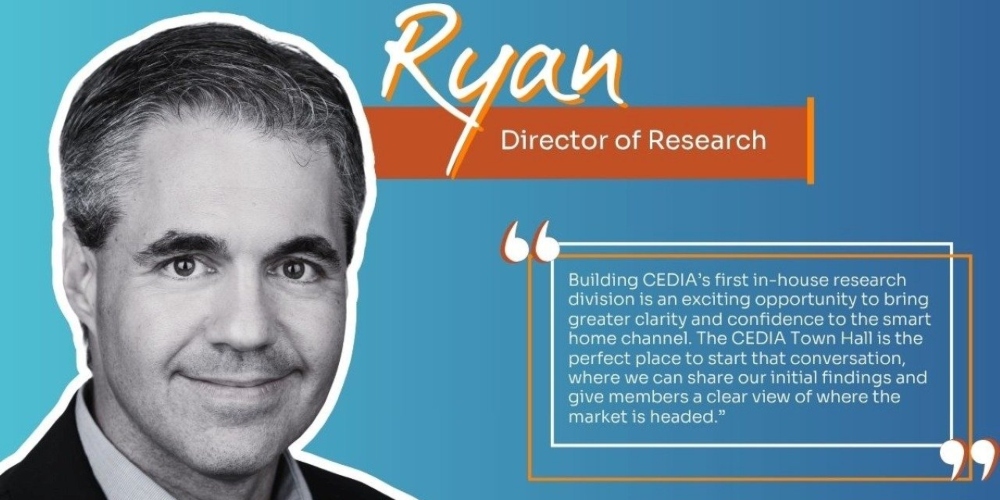
News May 6CEDIA Establishes Research Division to Bolster Industry Insight
The new division, headed by Ryan Bardach, will present its debut findings at CEDIA Expo 2026 during the…
News May 6Gramophone Purchases 70,000-Square-Foot Campus as New HQ, ‘Innovation Hub’
Located in Baltimore, Maryland, the complex is planned to host large-scale events while also housing multiple immersive showrooms…
News May 6JL Audio’s Primacy is a Dante-Powered, Auto-Optimizing Home Audio System
The full system, according to parent company Garmin, consists of a series of active tower or stand-mount loudspeakers…
News May 5AI-Generated Code Seen as Posing Several Risks to Smart Home Systems
Smart home enthusiasts and security experts are beginning to identify how AI-generated code may impact a smart home's…
News May 5Behind the Scenes: How CE Pro Editors Helped Curate the CEDIA Expo/CIX 2026 Smart Stage Sessions
CE Pro previews Smart Stage sessions at CEDIA Expo 2026, covering AI, energy, video walls, and business growth…
News May 4Graber Expands Motorization Alongside New Homestead, Monochrome Shade Designs
Graber’s 2026 Spring Collection updates several cellular, pleated and Roman shade designs with Somfy motorization while adding new…
News May 4How the FCC Policy on Foreign Routers Keeps Evolving: The Week in Playback
Peel back the noise of the news week with a relaxing spin through some of custom integration's biggest…
News May 3Inside Buzz Ep. 16: Clayton Ginn of Monitor Audio on High‑Performance Sound & Modern Applications
Monitor Audio shares insights on audio trends, product strategy, and integrator demand at CEDIA Expo/CIX 2025.
News May 1