The Latest
Filter by Topic
Filter by Type
How the FCC Policy on Foreign Routers Keeps Evolving: The Week in Playback
Peel back the noise of the news week with a relaxing spin through some of custom integration's biggest…
News May 3Inside Buzz Ep. 16: Clayton Ginn of Monitor Audio on High‑Performance Sound & Modern Applications
Monitor Audio shares insights on audio trends, product strategy, and integrator demand at CEDIA Expo/CIX 2025.
News May 1This New Accessory Retrofits Passive Speakers into Active Streamers: Wired In
Technology moves at a break-neck pace, and new releases can get lost in the shuffle. Keep up to…
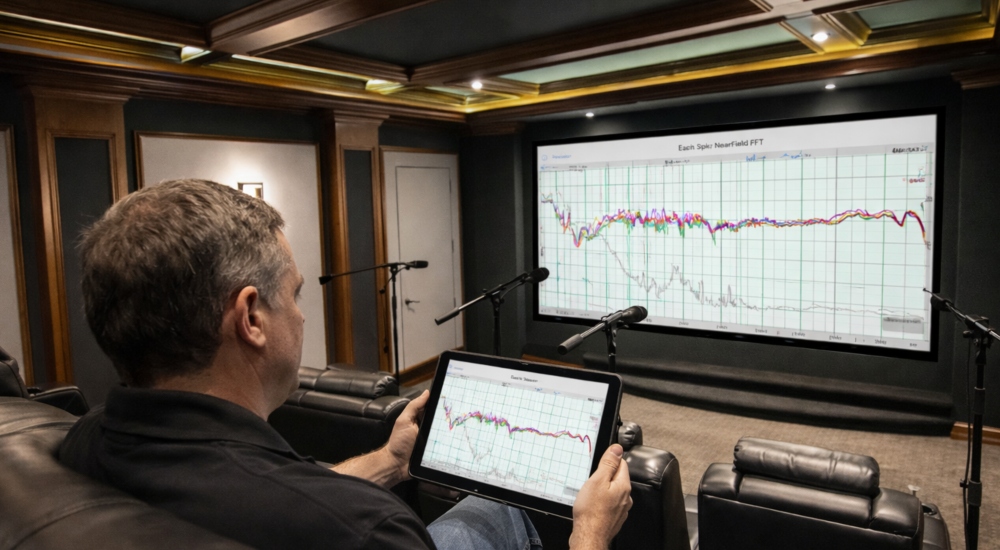
Products May 1HAA Link Looks to Make Room Calibration a Whole Lot Simpler for Integrators
The audio calibration software helps align integrators with the Alliance’s high-performance standards while also introducing a unified interface…
News May 1Google Gemini Update Highlights the Challenges LLMs Can Face in Smart Homes
A simple speed boost for Google’s Gemini assistant in Home reveals how the complexity of a smart home…
News May 1Axis Communications Opens Detroit Experience Center
The new location includes a security showcase as well as a dedicated testing lab for partners to evaluate…
News April 30CTA Urges FCC to Reconsider Software Update Cutoff in Foreign Router Policy
The association urges that under current policy, the March 2027 cutoff would create a significant number of vulnerabilities…
News April 30The Right Ingredients: A World-Renowned Chef’s Precision-Crafted Smart Kitchen
ZIO takes functionality to the extreme in designing a custom, luxury smart kitchen for a client who is…
Projects April 29Hotspots, Cellular Internet Devices Clarified to Be Banned Under FCC Router Policy
Updates to the FCC's FAQ page have revealed two devices not previously considered are now to be treated…
News April 29