The Latest
Filter by Topic
Filter by Type
The Week in Playback: ZION’s NA Debut, LG Rumors
Peel back the noise of the news week with a relaxing spin through some of custom integration's biggest…
News June 7Creating a Backyard Oasis with PureEdge Lighting
Utilizing a variety of PureEdge TruColor™ RGBTW architectural lighting systems, Technology Integrator Chase Goodman, owner of Cactus Sight…
Sponsored June 5C SEED’s Latest N1 Model Puts the Luxury of a Bugatti into a microLED TV
Working off the same technology as the original N1 folding TV, the new BUGATTI N1 brings in the…
News June 4JBL Closes Out Summit Loudspeaker Series with Flagship Everest and K2 Models
Being the fifth series to carry the “Project” moniker since JBL’s inception, the Summit Series represents the brand’s…
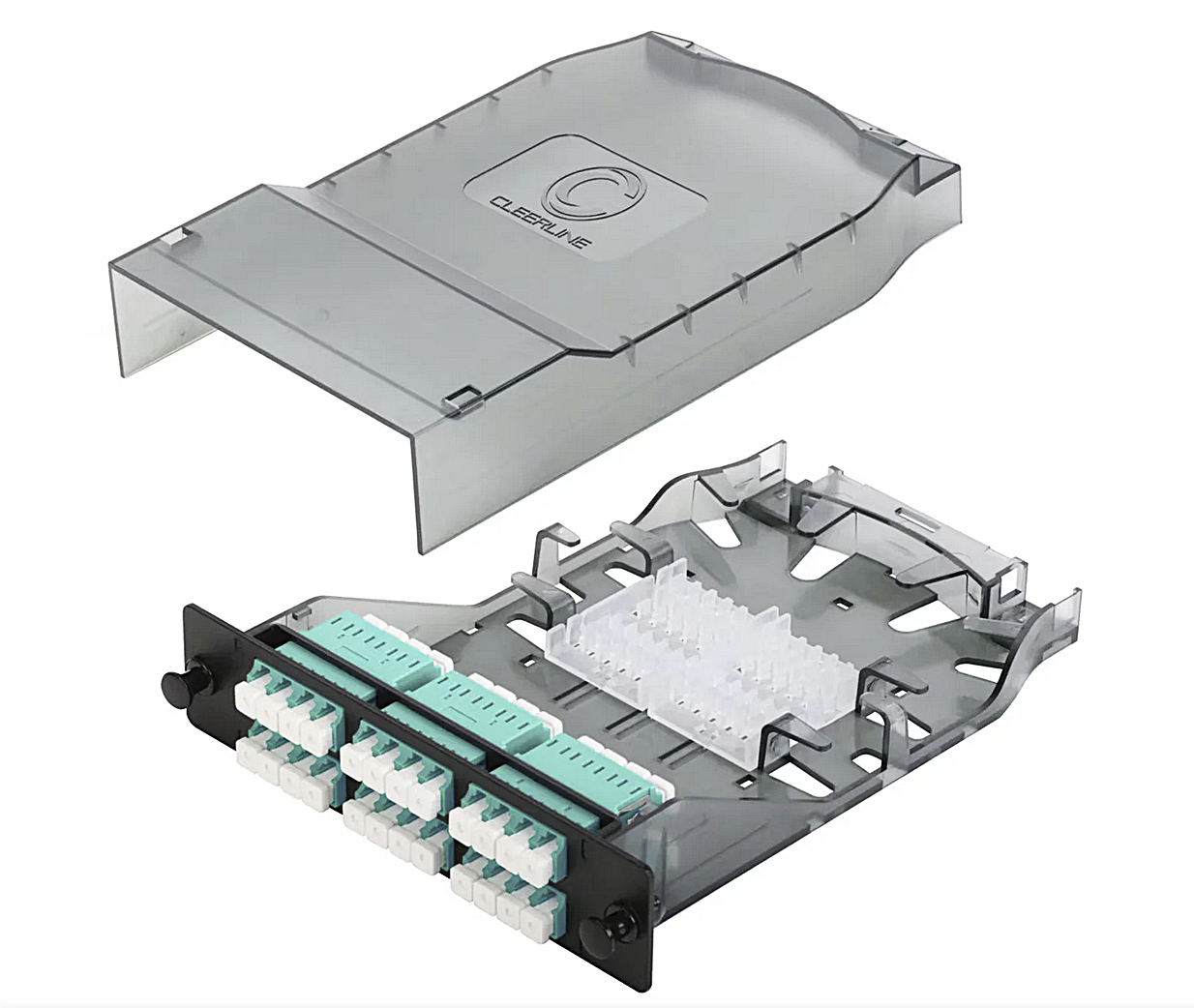
News June 4Cleerline HD Splice Cassettes for LGX Fiber
The Cleerline Technology Group has introduced a series of LGX-compatible fiber splice cassettes engineered to efficiently manage fusion-spliced…
Products June 4Genelec Launches Smart IP Controller 2.0 App for Loudspeakers
The latest app introduces a completely revamped user interface that aims to simplify control of smaller scale installations.
Briefs June 4Audio-Technica Names Annual Sales Rep Award Winners
The awards were presented by Jim Schanz, Audio-Technica Executive Director, System Solutions Sales, at an exclusive dinner at…
Briefs June 4Draper, Inc. Talks Heliotropic Shading and How It’s Reshaping Home Automation
Automatically managing shades throughout the day sounds simple in theory, but achieving the right balance of natural light,…
News June 3Nationwide Announces Programming and Registration for PrimeTime Nashville
The bi-annual event returns to Tennessee with continued focus on connection and the power of hospitality in business.
News June 3