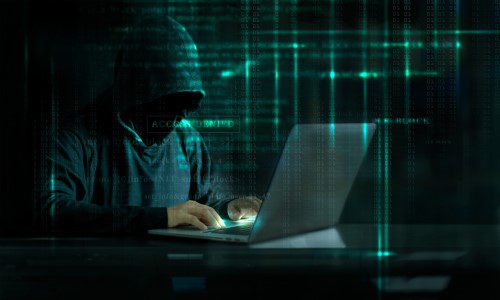
This past week has seen several instances of hackers seemingly speaking to people through their Ring security cameras. On Monday, NBC2 in Cape Coral, Fla. reported that a couple heard a voice spewing racial comments about their son through their camera.
Recently, KSHB4 posted a story about a woman in Wichita, Kan. that claims her Ring cameras were hacked when a voice talked to her and her children through their device. Also recently, Fox17 reported a woman in Memphis, Tenn. said a mysterious voice from her camera began taunting and harassing her 8-year-old daughter.
So what’s going on? The victims in Florida and Tennessee reached out to Ring which responded with the following:
Customer trust is important to us and we take the security of our devices seriously. While we are still investigating this issue and are taking appropriate steps to protect our devices based on our investigation, we are able to confirm this incident is in no way related to a breach or compromise of Ring’s security.
Due to the fact that customers often use the same username and password for their various accounts and subscriptions, bad actors often re-use credentials stolen or leaked from one service on other services. As a precaution, we highly and openly encourage all Ring users to enable two-factor authentication on their Ring account, add Shared Users (instead of sharing login credentials), use strong passwords, and regularly change their passwords.
-Ring
Using recycled log-in credentials is a common mistake that is frequently made with IoT devices and can lead to these types of incidents. This is because there is a pretty good chance these credentials have been exposed in a data breach.
However, there seems to be something more sinister afoot. Why the sudden rise in Ring camera hackings? After combing through different hacker crime forums, Motherboard has learned that hackers have developed a tool specifically for breaking into Ring accounts with cameras.
According to Motherboard, one forum has a post for a “Ring Video Doorbell Config.” A config is a file used to drive special software to quickly churn through usernames or email addresses and passwords and trying to use them to log into accounts.
One hacker is offering a Ring.com checker for $6. Another hacker even commented on how popular the tool is, saying, “I saw multiple people asking for this config.”
These incidents highlight the importance, and arguably necessity, for creating unique log-in credentials and enabling two-factor authentication for every account. Are you and your customers practicing cybersecurity best practices?
This article originally appeared on our sister publication Security Sales & Integration‘s website.